Sudomy serves as a subdomain enumeration tool designed to gather subdomains and analyze domains through advanced automated reconnaissance framework. Additionally, useful for OSINT (Open-source intelligence) activities. Its perfect tool for new bug bounter. Because for all recon you need to run many tools and collect the data. After while you may lost, forhet what you have don so far. But Sudomy is creating directories, files to understand all outputs.
Sudomy has unique and wonderful 20 features. You can read more detail here.
We will show most features on real target.
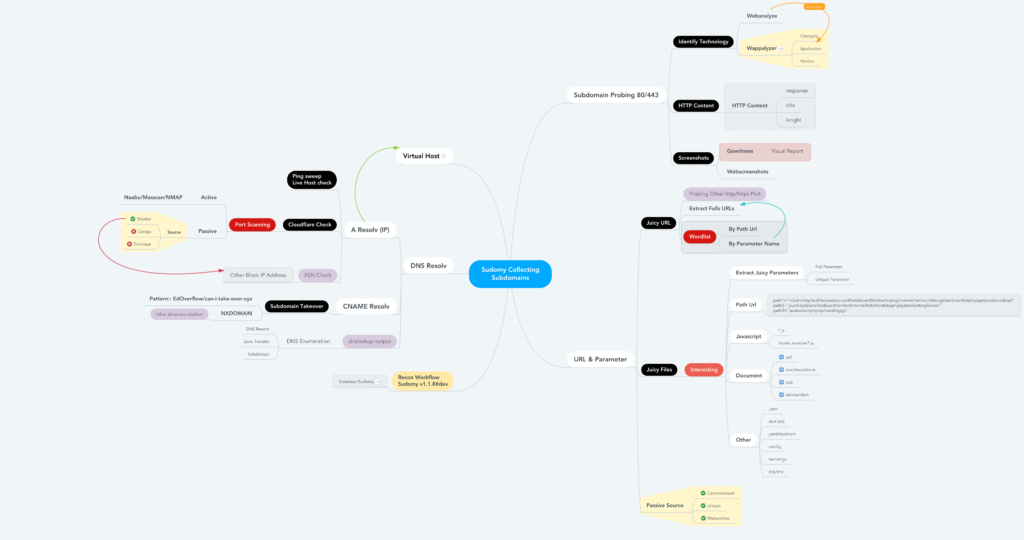
First of all, see below workflow. Better to check/anaylze/understand before directly jump into it.
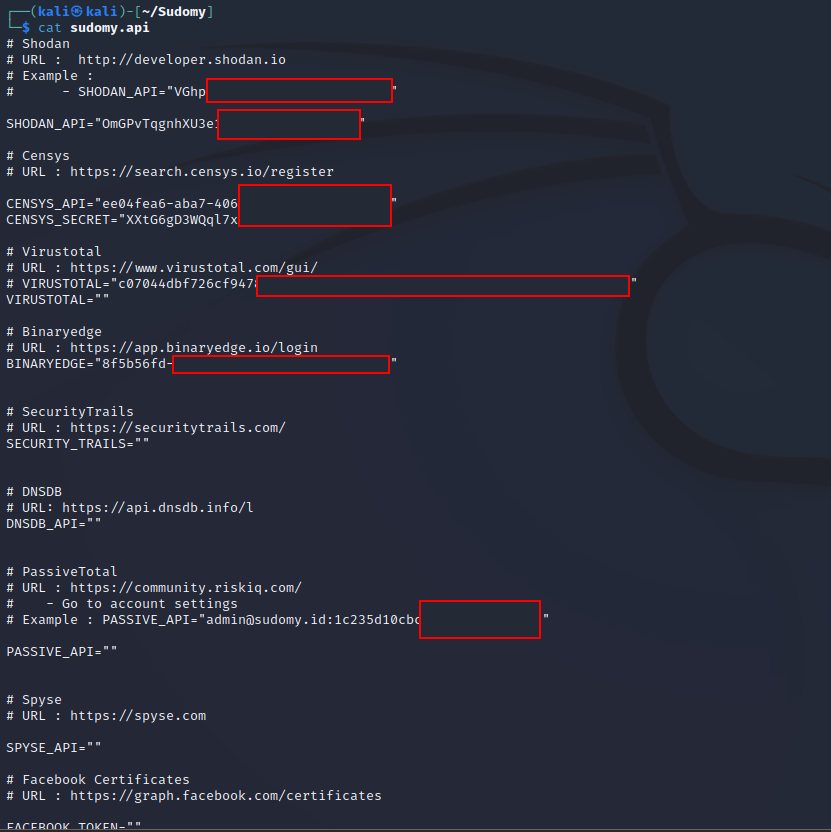
Make sure that you have set all API keys. Without API keys Sudomy cant query thir party sites. Well I dont have some of them. But at least you need Shodan, Censys, SecurityTrails
Also don’t forget dependencies/requirements.
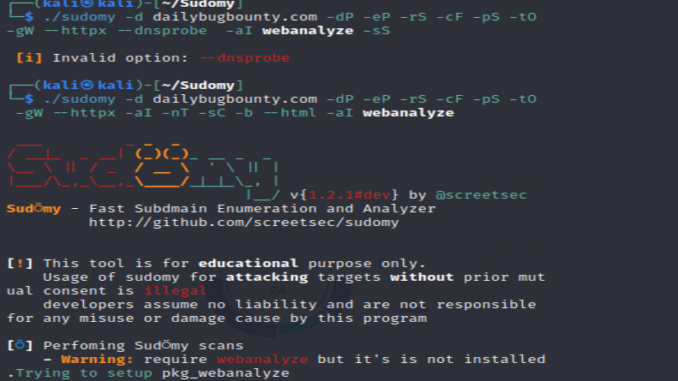
You can check all option with –help. I run the below options and see what its going to collect for us.
──(kali㉿kali)-[~]
└─$ cd Sudomy
┌──(kali㉿kali)-[~/Sudomy]
└─$ ./sudomy -d hackerone.com -dP -eP -rS -cF -pS -tO -gW –httpx -aI -nT -sC -b –html -aI webanalyze
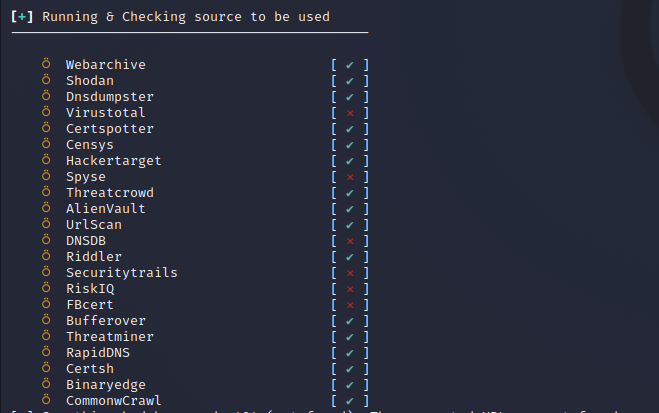
It will tell you if you dont have API keys.
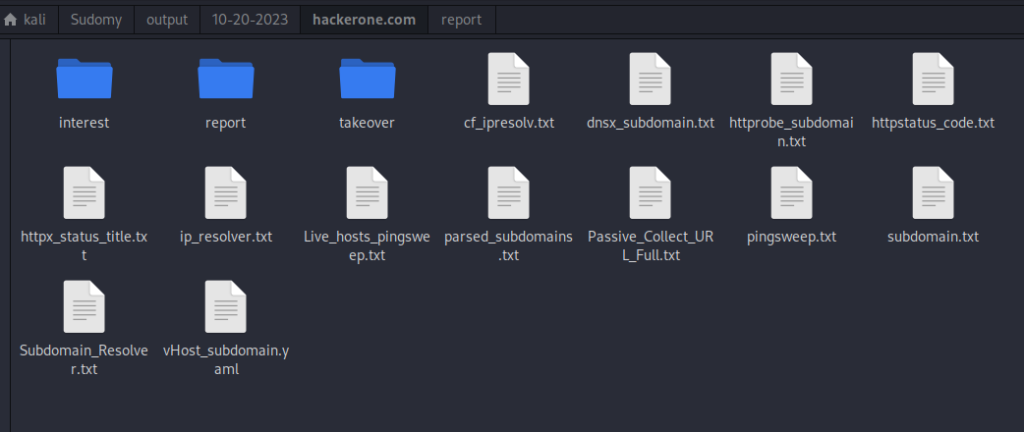
All output will be in Sudomy->output file.
And there is also user frinedly gui report. ->
/home/kali/Sudomy/output/../report
It summarizes all output.

Next step to find some bugs.
1.Check all alive domains manually if not too many. After that check interesting endpoint, sensitive endpoints, files, data. Read this article.
2.Try to scan all .js files. (Tools like js-miner, findsecret)
3.Check all url by greping “redirect=” “api” “token”, “@” ,“user” ,“logout”, “admin”, “number”, “redirect=” ,“.txt”
4.Run your custom nuclei teplates on all domains.
5. And do run all manuel tests on all domain, urls, endpoints.
Leave a Reply